Characterization of university drop-out at UNRN using data mining. A study case
Texto completo
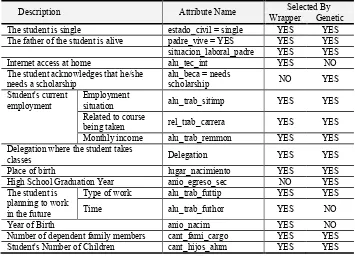
Figure


Documento similar
The article is organized as follows: Section II explains the general structure of the encryption system in the Ethernet physical layer 10GBase-R, Section III explains the
The structure of this paper is as follows. In Section 2, we introduce basic aspects of mobile agent technology, which is important for this work. In Section 3, we describe and model
The paper is organized as follows: in section 1 we state and prove the extrap- olation results, in section 2 we state the commutator theorems, these theorems are proved in section 4,
The observed data sample was used to calculate upper limits on the HSCP production cross section for each considered model and mass point.. The cross section upper limits at 95% CL
The paper is organized as follows: in Section 2, we provide the details of the numerical method, the initial and boundary conditions, including a description of the parameters used
The paper is organized as follows : Section 2 gives a brief introduction to the OOCSMP language, the C-OOL compiler and the mesh generator; section 3 describes the procedure to
The paper is organized as follows: section 2 presents an overview of our system; section 3 describes the extensions added to show different detail levels (an example of an
Section 2 develops the methodological proposal and describes the case study: Section 2.1 presents how the analysis was performed for 47 SUMPs carried out in Spain; the