An information security model based on trustworthiness for enhancing security in on line collaborative learning
Texto completo
Figure


Documento similar
The research presented in this paper includes a definition of a model of self-directed learning, an assessment method based on rubrics and questionnaires, and a development
This profile allows us to elicit security requirements in order to define an Access Control and Audit (ACA) model for DWs at the business
For this reason (and as we will show through- out this paper), we believe that if these security rules are specified on top of the underlying multidimensional model of the
The methodology developed for security management and its maturity in SMEs will allow any organization to manage, evaluate and measure the security of it information systems, but
Based on the papers, we establish an equilibrium model of the FCC supply chain in which a supplier and a retailer form an entirety based on collaborative replenishment, and act as
In this context, an alternative approach for on-line optimal maintenance management is proposed, based also on plant data rather than only on the decaying performance model..
Finally we observe that several types of analysis can be con- ducted on the models built with this approach: (i) a performance model with a set of security requirements can be
This paper describes the design and use of this crossword puzzle exercise and provides evidence on its usefulness for enhancing students’ intrinsic motivation and learning, as well



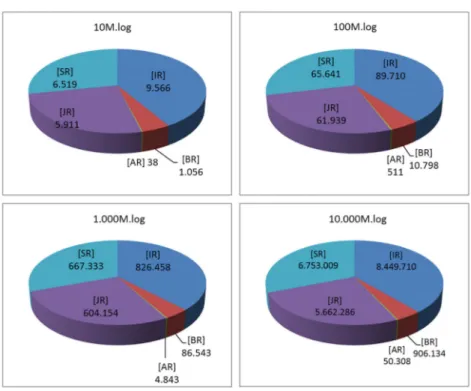
![Figure 1. Sequential processing of BSCW log files (A) [10] and local processing of UOC logs (B) [30].](https://thumb-us.123doks.com/thumbv2/123dok_es/7325435.356717/59.893.239.701.160.328/figure-sequential-processing-bscw-files-local-processing-uoc.webp)