Model selection using information criteria for hidden Markov principal components analysis
Texto completo
Figure
Documento similar
The proposed authentication system with protected tem- plates is based on the on-line signature verification sys- tem presented in [16], where a function-based approach is employed
Since the rules are applied to the host graph using injective matches only, and the GTS with a valid source model satisfies the Layered Graph Grammar Defi- nition (Def. 1), the
Experiment 2 showed that training is effective if the variance associated with the direction of the shots is consistently present in one body region but neutralized in others, and
Verification performance results are given for skilled forgeries with increasing number of training signatures: (a) training and testing signatures from different sessions, (b)
All signers in the database used for our experiments are man- ually assigned a legibility label and a type label. One of three different legibility labels is assigned: i) name
Mean absolute error (MAE) of the different forecasts: (i) initial competing forecasts (M1, M2, M3, M4, M5, M6 and M7 models) represented in grey color; NR has not been included in
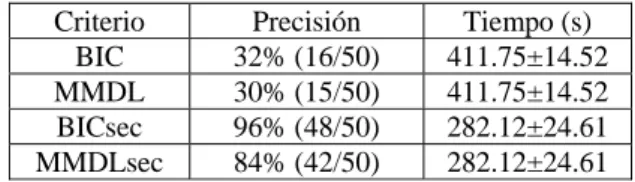
User-dependent Hidden Markov Models A recent study [10] has proven the benefits of using user-dependent models by specifically setting the num- ber of states and Gaussian mixtures
Algorithm 1 describes such calculation: for each possible configuration (line 4) calculates the weighted mean of the mean response time for each state combination of a provider